Managing digital certificates might sound simple, but for most organizations, it’s anything but not simple. For cryptography and IT teams handling hundreds of certificates, staying ahead of expirations, maintaining security, and meeting compliance demands are constant challenges. Here’s an in-depth look at why having robust certificate lifecycle management processes is essential, the obstacles organizations face, and how certificate lifecycle management practices help teams stay resilient.
According to Keyfactor, 77% of organizations have experienced outages due to unexpected certificate expirations, costing companies up to $72,000 per hour in downtime. This article breaks down the main issues teams face daily, from lost certificates and renewal overloads to navigating compliance audits.
TLS certificate lifecycles will shrink to 47 days by 2029
Manual certificate management increases security and outrage risks.
What’s Changed in Certificate Lifecycle Management Since 2024
The certificate lifecycle management landscape has shifted substantially in recent years. Three developments have converged to redefine what enterprise CLM readiness requires, each carrying direct implications for how security and IT teams must operate today.
The Road to 47 Days: From Apple’s Proposal to Binding Mandate
In 2024, Apple formally introduced a ballot proposing a phased reduction of maximum TLS certificate validity to 45 days. After refinement through forum discussion, the proposal passed as Ballot SC-081v3 on April 11, 2025 with Google, Mozilla, and Microsoft all endorsing the measure. The ballot establishes a three-phase reduction schedule: maximum validity drops to 200 days on March 15, 2026 (now in effect), to 100 days on March 15, 2027, and to 47 days on March 15, 2029. Domain control validation reuse will also be capped at 10 days by 2029. Phase 1 is already live, meaning any certificate issued after March 15, 2026 carries a 200-day maximum lifespan. Organizations still managing certificates manually are already contending with a doubled renewal workload, and that volume will increase sharply through each subsequent phase.
NIST Finalizes the First Post-Quantum Cryptography Standards
In August 2024, NIST published its first three official Federal Information Processing Standards (FIPS) for post-quantum cryptography, which are designed to replace legacy algorithms like RSA and ECC. These three standards, namely FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA), provide quantum-resistant replacements for RSA and elliptic curve algorithms, which underpin the X.509 certificates organizations manage today. A fourth standard, FIPS 206 (FN-DSA), remains in draft as of April 2026. Enterprises will eventually need to reissue certificates across their full inventory using quantum-resistant algorithms. Organizations with automated, crypto-agile CLM workflows are considerably better positioned to execute that migration than those dependent on manual processes.
The Entrust Distrust: A Case Study in CA Dependency Risk
In June 2024, Google announced it would stop trusting new TLS certificates issued by Entrust in Chrome, effective November 2024, citing a sustained pattern of compliance failures over six years. Apple and Mozilla issued their own distrust decisions shortly after. For organizations relying on Entrust-issued TLS certificates, the event required rapid discovery, replacement, and reissuance under tight timelines. Teams without centralized certificate inventory and automated workflows found the transition extremely difficult to complete in time. The incident remains the clearest real-world demonstration of why CA agility, the ability to migrate between certificate authorities without operational disruption, is a fundamental CLM requirement, not an optional capability.
What is Certificate Lifecycle Management?
Certificate Lifecycle Management refers to the processes involved in managing and overseeing each stage of a certificate’s lifecycle, from discovery and issuance to renewal and decommissioning.
For example, nearly every enterprise’s infrastructure includes external TLS/SSL certificates for secure web traffic, client certificates for secure system access, and device certificates for IoT endpoints. Managing these manually can lead to visibility gaps, security lapses, and costly outages. Centralized certificate lifecycle management ensures certificates are consistently managed, tracked, and monitored, significantly reducing risks.
However, proper certificate management goes beyond simply keeping your certificates up-to-date. A robust certificate management strategy consolidates oversight across environments, reduces human error, strengthens security, and supports compliance.
Types of Certificates and Their Unique Challenges
Different types of certificates serve unique functions, each with specific management requirements that add complexity to your certificate management solution.
- TLS/SSL Certificates: These are essential for secure web traffic and are among the most frequently renewed due to short lifespans. A lapse in TLS/SSL management risks customer trust and web application security.
- Code-Signing Certificates: Used to authenticate software integrity, these certificates are critical in development environments where unauthorized code could lead to vulnerabilities. Certificate management tools ensure these certificates are tracked and updated without disrupting the development process.
- Email Certificates (S/MIME): These secure email communications with encryption and signatures, critical for user privacy. Without certificate management tools, tracking each certificate’s lifecycle is challenging, especially when protecting sensitive email data.
- Device and Client Certificates: These certificates authenticate access for devices and users, commonly in IoT and internal applications. Certificate management tools monitor and update these certificates across distributed systems to prevent unauthorized access from rogue devices.
By centralizing certificate management, certificate management solutions help IT teams address each certificate’s specific requirements without missing renewals or risking security.
Why Today’s IT Landscape Demands Certificate Lifecycle Management
For cryptography and IT administrators, managing certificates goes beyond tracking a single certificate from issuance to revocation. Each type—be it TLS/SSL, code-signing, or device certificates—has unique management needs, which multiply as these certificates increase in volume and complexity. This life cycle includes discovery, issuance, monitoring, renewal, and decommissioning, all of which need consistent oversight across thousands of certificates in different systems.
With the average enterprise managing more than 25,000 certificates annually, it’s clear that tracking, renewing, and maintaining each certificate manually is impractical. The risk of “certificate sprawl” is high, with certificates scattered across cloud platforms, on-prem environments, and third-party applications.
The imminent shortening of TLS certificate validity periods from 398 to 90 or even 45 days compounds these challenges. The amount of work associated with each manually managed certificate is expected to increase 5 or even 10 fold. The expected need to switch to quantum ready certificates will compound this challenge even further. If you lack a robust CLM, you may be facing a massive, complex discovery, revocation, and reissuance process that could overwhelm your team, disrupt your operations, increase the risk of outages, and shake your customer’s confidence.
A robust certificate lifecycle management process centralizes certificate oversight, bringing every certificate under unified management, ensuring that no certificate is overlooked, and reducing costly disruptions.
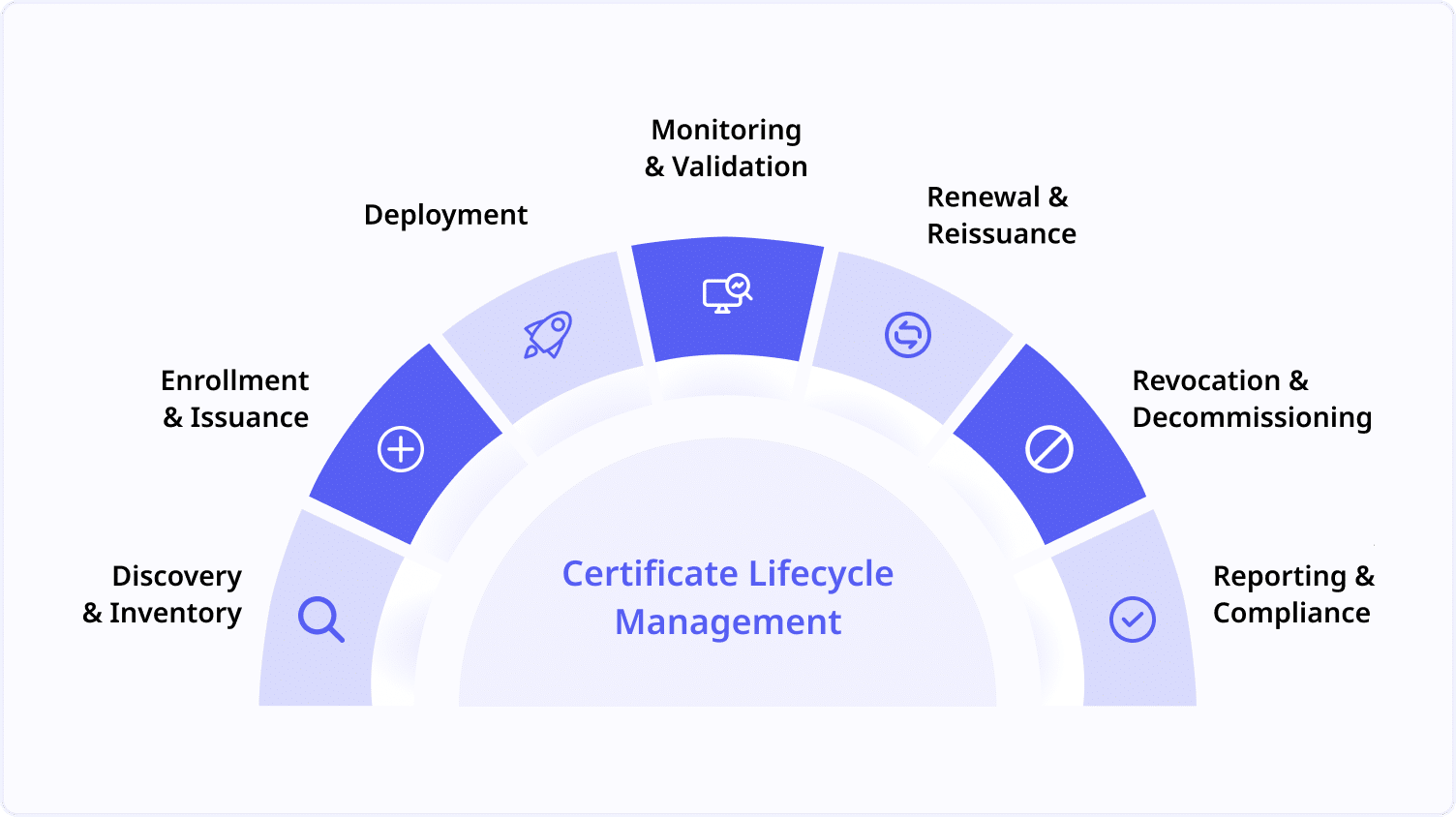
The 7 Stages of the Certificate Lifecycle Explained
Each stage in the certificate lifecycle requires careful attention to maintain visibility, strengthen security, and prevent costly downtime. Here’s how certificate lifecycle management keeps each phase on track:
- Certificate Discovery and Inventory: Finding every certificate across all environments is the first step. Automated discovery tools scan networks, bringing each certificate into a single inventory that provides a clear view of all certificate deployments. Research indicates that without active discovery, around 40% of expired certificates remain undetected, which can expose organizations to serious security risks. Certificate lifecycle management eliminates “ghost” certificates, giving IT teams a complete, organized inventory.
- Certificate Enrollment and Issuance: Requesting and obtaining new certificates starts with generating a Certificate Signing Request (CSR) and submitting it to a Certificate Authority (CA). Once issued, each certificate must be assigned to its designated owner and readied for deployment. This process can easily go awry if certificates are misassigned or left unmonitored. Certificate lifecycle management tracks each issuance, assigning ownership and making sure certificates land where they’re needed, without the guesswork.
- Certificate Deployment: Once issued, certificates must be configured and deployed to their intended servers, devices, or applications. Each system needs to recognize and use the certificate properly, whether it’s securing web traffic, authenticating users, or encrypting communication. Certificate lifecycle management supports seamless deployment across environments, so IT teams can be confident that certificates are installed correctly, preventing exposure from misconfigurations.
- Certificate Monitoring and Validation: Continuous monitoring ensures certificates stay active, healthy, and compliant. By tracking certificates in real time, certificate lifecycle management allows IT teams to identify and fix potential issues before they escalate into outages or security breaches. Automated alerts notify teams of expiring or compromised certificates, making it easy to stay ahead of disruptions and protect critical services.
- Certificate Renewal and Reissuance: All certificates have expiration dates, requiring regular renewal to avoid lapses in service. The renewal process often mirrors issuance, requiring a new CSR and approval from a CA. Managing renewals manually increases the chance of missed expirations. Certificate lifecycle management automates renewals, reissuing certificates seamlessly and minimizing human error so IT teams can focus on more critical tasks without fearing unplanned service interruptions.
- Certificate Revocation and Decommissioning: Sometimes certificates need to be revoked—perhaps due to security compromises or redundant credentials. Revoking removes a certificate from active use, while decommissioning retires it completely from the system. Without proper revocation, old certificates could create security risks. Certificate lifecycle management enforces revocation policies, making sure expired or unnecessary certificates are securely decommissioned, reducing unauthorized access risks.
- Certificate Reporting and Compliance: Reporting on certificate status and compliance is essential to both cybersecurity and operational success. With regular reporting, certificate lifecycle management offers insights into certificate health, usage, and compliance with internal policies or external regulations. Consistent logging and compliance reporting keep organizations audit-ready, simplifying the review process and helping IT teams stay aligned with evolving standards.
Operational Challenges in Certificate Lifecycle Management
1. Visibility Gaps and Ghost Certificates
When different departments manage certificates independently, some become “ghost certificates”—untracked and forgotten until they expire, creating security vulnerabilities. Certificate lifecycle management discovers and inventories all certificates, maintaining visibility and reducing risks of unplanned expirations.
2. Renewal Overload and Manual Processes
With shorter certificate lifespans, frequent renewals can become unmanageable when handled manually. Certificate lifecycle management automates renewals, issues proactive alerts, and keeps certificates up-to-date, freeing IT staff to focus on critical tasks rather than chasing renewals.
3. Fragmented Management Across Teams
In complex setups, different departments managing their own certificates lead to wasted resources and missed renewals. This siloed approach hinders consistent visibility. Certificate lifecycle management centralizes data into one dashboard, improving collaboration and ensuring up-to-date certificate status across the organization.
4. Compliance and Audit Complexity
Meeting regulatory standards requires precise documentation of certificate activities, which is challenging with disjointed tracking systems. Certificate lifecycle management automates audit-ready logs, providing a clear history of each certificate’s lifecycle, from issuance to revocation. This streamlines compliance and simplifies audit preparation.
5. Service Outages from Expired Certificates
Unexpected expirations disrupt critical applications, damaging customer trust. Certificate lifecycle management provides real-time monitoring and automated renewals, helping IT teams stay ahead of expiration dates and avoid outages impacting operations and reputation.
6. Preparing for Crypto-Agility
With advancing cryptographic standards, IT teams must regularly update certificates to maintain security, especially as quantum computing becomes more feasible. Manually updating certificates is time-intensive and prone to errors. Certificate lifecycle management with crypto-agility capabilities enables smooth transitions to new encryption standards, future-proofing security.
302% ROI from Modernizing Certificate Lifecycle Management
Learn why organizations are automating certificate governance and renewals to reduce outages and improve security.
Choosing the Right Certificate Management Solution
For IT teams grappling with certificate sprawl, unexpected expirations, and complex hybrid environments, the below CLM platforms provide robust features, such as automated certificate discovery, renewal workflows, and centralized management dashboards. When evaluating certificate management solutions, consider factors like the level of automation, compatibility with multi-cloud environments, and integration with broader security systems.
- CyberArk | Venafi TLS Protect
Venafi TLS Protect, now part of the CyberArk, offers enterprise-grade certificate lifecycle management across on-premises, cloud, and hybrid environments. It provides centralized visibility into TLS machine identities, automated discovery and renewal workflows, and policy enforcement across certificate issuance. For organizations that have already invested in CyberArk for privileged access management, the combined platform enables a unified approach to both human and machine identity security, managing certificate risk within the same governance framework that governs privileged credentials.
- Keyfactor Command
Keyfactor Command delivers PKI and CLM automation with flexible deployment options for on-premises, SaaS, and fully hosted, making it adaptable to the infrastructure constraints of diverse enterprise environments. It supports certificate discovery, issuance, renewal, and revocation across multiple CAs, and integrates with DevOps pipelines, ITSM platforms, and cloud services. Keyfactor is particularly well-suited for organizations with complex enterprise PKI requirements, IoT or device identity challenges, or code signing governance needs. Its deployment flexibility also makes it a practical choice for regulated industries where data residency and infrastructure control are non-negotiable.
- AppViewX CERT+
AppViewX CERT+ provides full certificate lifecycle management with a strong emphasis on workflow automation, multi-CA support, and cryptographic posture management. Its automation engine enables teams to orchestrate certificate provisioning, renewal, and revocation across complex, multi-platform environments without manual intervention. AppViewX is particularly relevant for organizations preparing for the 47-day certificate mandate and post-quantum cryptography migration, where identifying weak algorithms, enforcing certificate policies across multiple issuers, and automating at scale are essential requirements. For organizations building a long-term, crypto-agile CLM strategy, AppViewX’s posture management capabilities provide a level of visibility that few platforms match.
- Sectigo Certificate Manager
Sectigo Certificate Manager (SCM) provides enterprise CLM for both public and private certificates, combining a broad CA portfolio with automation capabilities that support the ACME protocol for public TLS certificate issuance and renewal. Following Sectigo’s acquisition of Entrust’s public certificate business in January 2025, its enterprise customer base and CA infrastructure expanded significantly, making it a more prominent option for organizations managing large-scale public certificate environments. Sectigo is well-positioned for organizations seeking competitive pricing on public certificates alongside centralized lifecycle management and multi-CA governance.
- Entrust PKI and Certificate Management
Entrust provides enterprise PKI infrastructure and certificate management capabilities suited to organizations operating private certificate environments in high-assurance contexts. Their platform supports private CA deployment, internal certificate issuance, and lifecycle management, complemented by their nShield HSMs, which provide FIPS 140-2/140-3 validated cryptographic foundations for enterprise PKI operations. For organizations that require tightly governed, internally managed certificate infrastructure rather than dependence on public CA issuance, Entrust offers a mature, compliance-oriented platform with a long track record in regulated industries.
CLM Vendor Comparison: Platforms at a Glance
The table below provides a side-by-side comparison of the CLM platforms covered in this guide, mapped to the criteria most relevant to enterprise certificate management decisions.
| CLM Platform | Deployment Model | CLM Differentiation | Certificate Types Supported | Best Fit For | Accutive Partner Status |
| CyberArk | Venafi
TLS Protect / Control Plane |
Cloud, On-Prem, Hybrid | Unified machine identity platform combining CLM with PAM and secrets management under a single governance framework. Strong at enterprise scale across multi-cloud and DevOps environments. ACME-supported automation via the Venafi Control Plane. | TLS/SSL
Code Signing SSH Certificates IoT / Device Private PKI |
Large enterprises managing machine identities at scale; organizations with existing CyberArk PAM investment seeking unified human and machine identity governance across a single platform | Certified Partner |
| Keyfactor
Command + EJBCA |
Cloud (PKIaaS), On-Prem, Hybrid | Tight integration between enterprise CLM (Command) and CA (EJBCA), providing end-to-end PKI and certificate management from a single vendor. Purpose-built code signing governance via Signum. Recognized for strong IoT and device identity capabilities at scale. | TLS/SSL
Code Signing IoT / Device Private PKI |
Organizations with complex enterprise PKI requirements; teams with code signing governance needs; regulated industries requiring flexible deployment models and full control over PKI infrastructure | Certified Partner |
| AppViewX
CERT+ |
Cloud, On-Prem, Hybrid | Automation-first CLM with workflow orchestration across multi-CA, multi-platform environments. Delivers cryptographic posture management — identifying weak algorithms, misconfigured CAs, and expiring certificates enterprise-wide. The strongest platform for 47-day mandate readiness and post-quantum migration planning. | TLS/SSL
Code Signing IoT / Device Private PKI |
Organizations preparing for the 47-day certificate mandate; DevOps-heavy certificate environments; enterprises prioritizing crypto agility, cryptographic posture visibility, and PQC migration readiness | Certified Partner |
| Sectigo
Certificate Manager (SCM) |
Cloud (SaaS), Hybrid | Broad commercial CA portfolio combined with enterprise CLM, with strong ACME support for public TLS automation. Expanded enterprise customer base and CA infrastructure following acquisition of Entrust’s public certificate business in January 2025. Competitive pricing for public certificate volume. | TLS/SSL
Code Signing S/MIME IoT / Device Private PKI |
Organizations managing large volumes of public TLS certificates; teams seeking competitive CA pricing alongside centralized lifecycle management and ACME-based automation | Resale Partner |
| Entrust
PKI and Certificate Management |
Cloud, On-Prem, Hybrid | Enterprise private PKI and CA management with deep nShield HSM integration. FIPS 140-2/140-3 validated cryptographic foundations. Compliance-oriented platform purpose-built for high-assurance private certificate environments in regulated industries. | TLS/SSL
Code Signing S/MIME IoT / Device Private PKI |
Regulated industries requiring tightly governed private certificate infrastructure with HSM-backed key management; government, financial services, and healthcare environments where compliance assurance is a primary selection criterion | Certified Partner |
Selecting the Right Fit with Accutive Security
Accutive Security operates as a Center of Excellence in Cryptography, Identity Security, and Data Protection, maintaining certified implementation expertise across the leading CLM platforms rather than representing a single vendor. This means our solution guidance is grounded in direct delivery experience: we assess your infrastructure, compliance requirements, and operational model to identify the right fit based on your specific context, not sales incentive.
For organizations that require hands-on validation before committing, our Innovation Lab provides a purpose-built environment where your team can build and test realistic proof-of-concept deployments across platforms. Rather than relying on vendor-led demos, the Innovation Lab lets you evaluate real-world performance against your own environment and requirements, reducing procurement risk and accelerating decision-making.
Not sure which CLM platform fits your environment?
Accutive Security’s team has implemented Venafi, Keyfactor, AppViewX, and Entrust across enterprise environments in financial services, healthcare, and the public sector.
Talk to an Expert
Considerations When Implementing Certificate Lifecycle Management
Implementing certificate lifecycle management can transform how your organization handles security and compliance, but certain hidden challenges can impact its success. By identifying these key considerations early on, IT teams can ensure a smoother, more effective rollout and ongoing management of certificate lifecycle management.
- Scaling with Growing Certificate Volume
As digital assets expand, so does the certificate load, and not all certificate lifecycle management solutions can handle high volumes seamlessly. Without the right system, scaling up can lead to performance issues or bottlenecks. Look for certificate lifecycle management designed to manage substantial certificate volumes, ensuring smooth operations as your digital footprint grows - Integration with Legacy Systems
Many organizations rely on legacy systems that don’t always integrate smoothly with newer tools. Certificate lifecycle management solutions with strong API support or integration capabilities can bridge these gaps, allowing IT teams to manage certificates effectively across both legacy and modern environments, ensuring nothing slips through the cracks. - Managing Mixed Environments
Hybrid, multi-cloud, and on-premises setups introduce complexity to certificate oversight, often resulting in siloed certificates. This fragmented approach can lead to visibility gaps, making it harder to monitor certificate health across the board. Choose a certificate lifecycle management solution that offers centralized visibility across all environments, making it easier to track and manage certificates wherever they reside. - Human Error and Setup Complexity
Even with automation, certificate lifecycle management systems can be complex to set up and maintain. Misconfigurations during setup or routine maintenance can lead to security vulnerabilities or operational issues. A certificate lifecycle management solution with a user-friendly interface, role-based access control (RBAC), and detailed onboarding resources helps reduce these risks, enabling IT teams to operate securely and efficiently. - Addressing Shadow IT and Unaccounted Certificates
Shadow IT—certificates issued outside the IT team’s oversight—can introduce significant security risks. With periodic discovery scans, a robust certificate lifecycle management solution brings rogue certificates under management, reducing unauthorized access points and helping IT teams gain full control over the certificate landscape. - Leveraging Analytics for Better Management
Integrating analytics into your certificate lifecycle management system provides actionable insights that go beyond simple tracking. Analytics on certificate usage, expiration, and renewal patterns help IT teams anticipate needs, allocate resources efficiently, and prevent overloads from a surge of renewals.
Taking these considerations into account ensures that your certificate lifecycle management system is set up for success, providing lasting security benefits and empowering your IT team to manage certificates efficiently across your entire infrastructure
Demonstrating ROI from Certificate Management Tools
Implementing a certificate lifecycle management solution requires an upfront investment, and proving its ROI can be challenging, especially when the savings are indirect. However, a well-integrated certificate lifecycle management system can deliver a 4-10x return by preventing costly security incidents and streamlining everyday operations.
Certificate lifecycle management is more than just another tool; it’s a strategic way to secure your organization’s infrastructure and keep things running smoothly. But to get the most from it, especially in complex setups, you need a solution that fits your organization’s specific needs, not a one-size-fits-all approach.
That’s where experts like Accutive Security make the difference. Rather than just implementing a certificate management tool, they tailor it to your organization’s specific infrastructure, compliance needs, and security goals. By aligning your certificate management tool with your regulatory requirements, hybrid systems, and day-to-day processes, Accutive Security ensures the system isn’t just running in the background—it’s seamlessly integrated into workflows in a way that actually makes work easier.
Conclusion: Turning Certificate Lifecycle Management into a Strategic Advantage
Managing digital certificates is no longer just an item on the IT to-do list; it’s a foundational element of securing digital infrastructure and ensuring operational continuity. The right certificate management approach enables IT teams to not only stay ahead of expirations and compliance demands but also anticipate and solve the hidden issues that often get overlooked.
With Certificate Lifecycle Management, IT gains centralized control over certificates across environments, supporting security frameworks like zero-trust, where every certificate is verified to minimize access risks. As cryptographic needs evolve, Certificate Management ensures readiness, enabling smooth transitions to new standards without compromising security.
Key Takeaways:
- Enhance Uptime: Proactive monitoring and real-time alerts reduce downtime, keeping services uninterrupted.
- Strengthen Security: Centralized control supports zero-trust principles and secure certificate interactions across systems.
- Future-Proof Operations: CLM adapts to new cryptographic standards, ensuring long-term data protection.
Certificate lifecycle management, when done right, becomes a strategic advantage. It gives IT teams the tools to unify certificates across legacy and modern environments, actively mitigate downtime risks, and seamlessly adapt to emerging cryptographic standards.
Ultimately, certificate management helps IT teams breathe easier. Instead of constantly reacting to certificate problems, they can focus on building a robust, future-ready infrastructure. For organizations that rely on secure, uninterrupted operations, certificate management isn’t just helpful; it’s transformative.
Frequently Asked Questions About Certificate Lifecycle Management
What is Certificate Lifecycle Management?
Certificate Lifecycle Management (CLM) is the set of processes, policies, and technologies used to manage digital certificates from initial discovery through final revocation. It covers every operational stage: discovering existing certificates, requesting and issuing new ones, deploying them to their intended systems, monitoring for expiration or compromise, renewing them on schedule, revoking them when necessary, and maintaining audit-ready records throughout. CLM ensures that no certificate is overlooked, expired, or mismanaged.
What are the stages of the certificate lifecycle?
The certificate lifecycle consists of seven stages. Discovery and inventory: identifying all certificates across the environment. Enrollment and issuance: requesting and obtaining new certificates from a Certificate Authority. Deployment: configuring and installing certificates on their intended servers or devices. Monitoring and validation: tracking certificate health and expiration in real time. Renewal and reissuance: replacing certificates before they expire. Revocation and decommissioning: retiring certificates that are compromised or no longer needed. Reporting and compliance: maintaining audit logs and policy documentation.
What is the difference between CLM and PKI?
Public Key Infrastructure (PKI) is the framework that makes digital certificates possible: the Certificate Authorities, trust hierarchies, policies, and cryptographic standards that govern how certificates are issued and validated. CLM is the operational layer that manages what PKI produces. An organization can have a mature PKI environment and still experience certificate-related outages if it lacks the processes to track, renew, and govern those certificates at scale. While PKI defines the rules, CLM enforces them operationally.
How many digital certificates does an enterprise typically manage?
More than most organizations realize. According to Keyfactor’s 2023 State of Machine Identity Report, the average enterprise manages approximately 256,000 internally trusted certificates, a figure that has grown consistently year over year as cloud adoption, containerization, and IoT expand the machine identity surface.
What happens when a TLS certificate expires?
When a TLS certificate expires, browsers immediately flag the affected site as untrusted, presenting users with a full-page warning that blocks access. For internal services, APIs fail, application integrations break, and dependent workflows stop functioning.
Do I need a CLM platform if I already use ACME?
ACME is a protocol, not a platform. It automates certificate issuance and renewal for supported Certificate Authorities and compatible endpoints, but it does not provide centralized discovery, multi-CA governance, compliance reporting, or policy enforcement. It also does not cover certificate types outside its scope, including code signing, S/MIME, and many private PKI use cases. A CLM platform integrates ACME as one automation layer within a broader system that addresses the full operational complexity of enterprise certificate infrastructure.
How will the 47-day certificate mandate affect CLM operations?
The move to 47-day maximum TLS certificate validity increases renewal frequency by more than eightfold compared to the previous 398-day standard. By 2029, domain control validation will also need to be repeated every 10 days. Manual renewal workflows are operationally unsustainable at this cadence. CLM platforms with ACME support and automated policy enforcement are shifting from recommended tooling to essential infrastructure for any organization managing public TLS certificates.
What is crypto agility and why does it matter for CLM?
Crypto agility is the ability to replace deprecated cryptographic algorithms across an organization’s systems rapidly without significant architectural disruption. It matters for CLM because certificates embed specific algorithms and when those algorithms are deprecated, every dependent certificate must be reissued. The post-quantum migration is the most consequential pending example: NIST finalized its first three post-quantum cryptographic standards (FIPS 203, 204, and 205) in August 2024, and enterprises will eventually need to reissue certificate inventories using quantum-resistant algorithms. CLM automation is what makes that migration executable at scale.
Certificate lifecycles are getting shorter
Organizations are shifting towards automated certificate governance and renewal management.












Leave a Reply